MACCDC takes great pride in being one of the premier events of this type in the world.
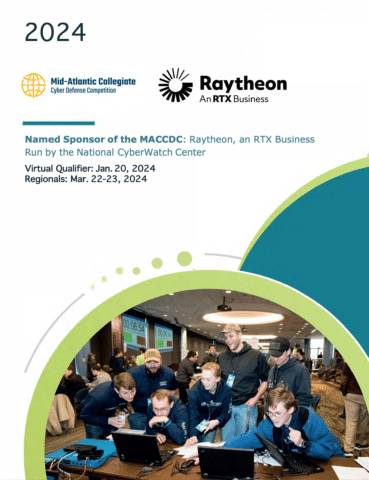
The 2024 Mid-Atlantic Collegiate Cyber Defense Competition (MACCDC) is in its 19th year of providing a unique experience for college and university students to test their cybersecurity knowledge and skills in a competitive environment. In 2023, more than 200+ students competed for an opportunity to be one of eight teams to advance to the Regional Finals. The winner of the MACCDC represents the Mid-Atlantic region at the National CCDC, usually the third week in April.
“Such experiential education increases the knowledge and expertise of future professionals who may be in a position to contribute to the secure design and operation of critical information and its supporting infrastructure.”
from Exploring a National Cyber Security Exercise for Colleges and Universities, Lance J. Hoffman and Daniel Ragsdale, 2004
While similar to other cyber defense competitions in many aspects, MACCDC, as part of the National CCDC, is unique in that it focuses on the operational aspects of managing and protecting an existing network infrastructure. Teams are physically colocated in the same building. Each team is given physically identical computer configurations at the start of the competition. Throughout the competition, the teams have to ensure that the systems supply the specified services while under attack from a volunteer Red Team. In addition, the teams have to satisfy periodic “injects” that simulate business activities IT staff must deal with in the real world.
In spring 2006, five teams from Maryland, Virginia, and Pennsylvania competed in the 1st MACCDC. By today’s standards, the infrastructure was simple. Each team had a router, a firewall, and a small sampling of servers. Scoring was accomplished through a custom Perl script that checked network and service availability and integrity. In 2006, the teams defended a mere seven assets, including a router, a firewall, servers, and an IP surveillance camera, and there were only four Red Team members (“hackers”) attacking and disrupting the students’ infrastructure.
The Teams: Red vs. Blue
Team Objectives
- Build a meaningful mechanism by which institutions of higher education may evaluate their programs.
- Provide an educational venue in which students are able to apply the theory and skills they have learned in their course work.
- Foster a spirit of teamwork, ethical behavior, and effective communication both within and across teams.
- Foster a dialog and awareness among participating institutions and students.
Competition Terminology
Gold Team
Competition officials who organize, run, and manage the competition
White Team
Competition officials who observe team performance in their competition area and evaluate team performance and rule compliance
Red Team
Penetration testing professionals simulating external hackers attempting to gain unauthorized access to competition teams’ systems
Black Team
Competition support members who provide technical support, pick up and deliver communications, and provide overall administrative support to the competition
Blue Team
The institution competitive teams consisting of students competing in a CCDC event
Team Captain
A student member of the Blue Team identified as the primary liaison between the Blue Team and the White Team
Team Co-Captain
A student member of the Blue Team identified as the secondary or backup liaison between the Blue Team and the White Team, should the Team Captain be unavailable (i.e., not in the competition room)
Team Representatives
A faculty or staff representative of the Blue Team’s host institution responsible for serving as a liaison between competition officials and the Blue Team’s institution
Organizing Team
Casey O’Brien

Casey is a co-founder of the MACCDC and Co-Principal Investigator of the National CyberWatch Center, the organization behind the MACCDC since its inception in 2006.
Dr. Joel Koudjo Koumadi

Dr. Koumadi has been involved with the MACCDC since 2023, assuming the Regional Director role in 2024. He is also a Professor of Networking and Cybersecurity in the Technology, Engineering, and Construction (TEC) Department at Prince George’s Community College in Largo, MD.
Why Get Involved?
Students who compete in MACCDC will, no doubt, come away with information security skills way beyond those of the average IT specialist. The CCDC is also a great way to bolster your resume by:
- Bringing attention to your qualifications and experiences
- Networking with representatives from leading corporations and federal agencies
- Gaining hands-on experience hardening network assets against live, constant threats
- Attending featured keynote speeches by industry leaders